ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]
Regular price
$12.00
Sale
- ICERS is a digital product that is downloaded upon purchase.
- Includes a .docx editable template. (.pdf and .odt files also available upon request)
- Free lifetime updates as we continue to modify ICERS to adjust to current threats and developments.
This is a template designed to be filled out now and then implemented following an emergency.
ICERS outlines a means to plan for life altering events, SHTF, in order to maintain communications among family & friend’s households while assessing sustainability to determine when to shelter in place, bugout, or pool resources. While contact among households is key, ICERS creates 3 incident based Categories with a set of actionable plans when comms are down. The Actions work in concert with predefined Rally Points and “What If” scenarios so that all affected parties can reunite or self-sustain.
BOTTOM LINE UP FRONT (BLUF):
- ICERS is composed of multiple House Holds (HHs) working together to support one another. Each may be subject to various Life Altering Events (LAEs) and each may have a varying degree of experience, resources, and security. ICERS works to utilize the HHs strengths to ensure all are prepared to act when an LAE occurs.
- During an LAE; If comms are established disregard all plans and formulate actions based on current knowledge.
- If comms are down; refer to the Categories (CATs).
- Identified your current CAT, initiate the Action Plan (AP) for that CAT.
- Action Plans create an order of precedence for how to make contact, when to bug out, and what steps to take as time progresses.
- Action Plans incorporate meeting at Rally Points (RPs) or following the Bug Out Guideline (BOG) during pre-planned “What If” scenarios. The end goal of ICERS is to reestablish contact, find resources, and appropriate shelter.
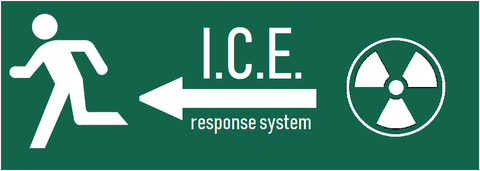
- Add the ICERS Quick Reference Decal to your order here.
SO WHAT ACTUALLY IS ICERS?
It's a document. It allows you to have a quick reference for phone numbers and addresses for your family and prepping team. It has guidelines to follow for when a crisis occurs so that you know when to shelter in place or where to bugout . The document's primary focus is making sure all members know what to do even if they are unable to talk to each other due to cellular outages. It's a template you complete now, download/print, then refer to when things go bad.
How to get started: When you download your copy you will need to sit down with your trusted households and friends to formulate the plan and record it into ICERS. 1. Decide who's in your circle and assign callsigns. 2. Collect contact information. 3. Determine "Rally Points". 4. Develop "What If" Scenarios for threats specific to your group. 5. Agree upon a communication code. 6. Save and distribute mastercopy, download, and print; then securely store until needed. 7. Keep full copies in you Bugout Bag, Truck, Home Lockbox; keep quick reference cards on your person. 8. When crisis strikes refer to ICERS.
///
If you were impacted by Hurricane Helene, download and print a free copy of ICERS with code HELENE.
If you were not impacted and want to help, purchase ICERS for the standard $12 price and we'll donate the entirety to the North Carolina Disaster Relief Fund via nc.gov/donate (you get ICERS and we donate all the proceeds for October).

![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/files/1717896698141_530x.png?v=1762525599)
![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/files/1717896698141_160x.png?v=1762525599)
![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/products/1603659202344_160x.jpg?v=1717898168)





![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/products/1603616258450_160x.png?v=1717898168)





![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/products/20200126-114934-02_d728d3ff-389e-4584-9ed4-7c3530a0139d_160x.jpg?v=1717898168)
![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/products/Screenshot-20200221-103724-Docs-01_160x.jpg?v=1717898168)

![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/products/Bazaart_20201025_044328_160x.png?v=1717898168)
![ICERS - In Case of Emergency Response System and Bugout Plan [Digital Folder]](http://www.superessestraps.com/cdn/shop/products/1631606166730_160x.png?v=1717898168)